What Is the Advanced Encryption Standard? AES Explained
The beauty of digital encryption is that it keeps sensitive and private data hidden, even in the face of a ransomware attack or a data breach. Without the cipher, or key, to decrypt data, criminals aren’t able to decipher files. It’s one of the most basic elements of cyber security.
Today, the Advanced Encryption Standard (AES) is the standard encryption method for industries and functions from retail to finance.
At Macrium, we use AES to protect our users’ files from accidental deletion and malware, such as ransomware. So, we’ve put together this guide for those wondering how AES originated and became the encryption standard of choice.
What Is AES?
AES is an algorithm developed by two Belgian cryptographers, Vincent Rijmen and Joan Daemen. The duo submitted it in response to a call from the National Institute of Standards and Technology (NIST) to the cryptography community.
NIST challenged specialists in the field to create an updated encryption standard to meet the growing security needs of the 21st century. The previous standard, Data Encryption Standard (DES), developed by IBM in the 1970s, was failing to keep up with advancements in computing technology.
AES was formally adopted by NIST in 2001. Today, it’s one of the most popular encryption standards around the world, thanks to its speed and security.
Why Is It Important to Understand AES?
Since AES is one of the most widely used encryption standards, it’s important to know how it works to make informed decisions about data security and risk management. This is especially true for businesses in highly regulated fields that handle sensitive information, such as finance, healthcare and the military.
Most businesses and organizations must comply with industry and national standards, regulations and legislation regarding data security and privacy. Understanding AES can help them do so, reducing their risk of facing penalties or other consequences for failure to comply.
Finally, understanding the principles of AES and the protection it offers from hackers and attacks supports confidence in its reliability and provides peace of mind.
How Does AES Work?
AES is a symmetric method of encryption, meaning the same key is used to encrypt and decrypt data. However, unlike older symmetric methods, AES splits data into blocks of 128 bits each. The blocks go through several rounds of different types of transformation, such as substitution, shifting, and transposition.
This makes AES extremely secure from a brute-force attack. It presents a nearly incomprehensible number of possible combinations that would take billions of years to decrypt using current computing power and technology.
AES uses key lengths of 128, 192, and 256 bits, with 256 being the strongest. Each goes through a different number of rounds.
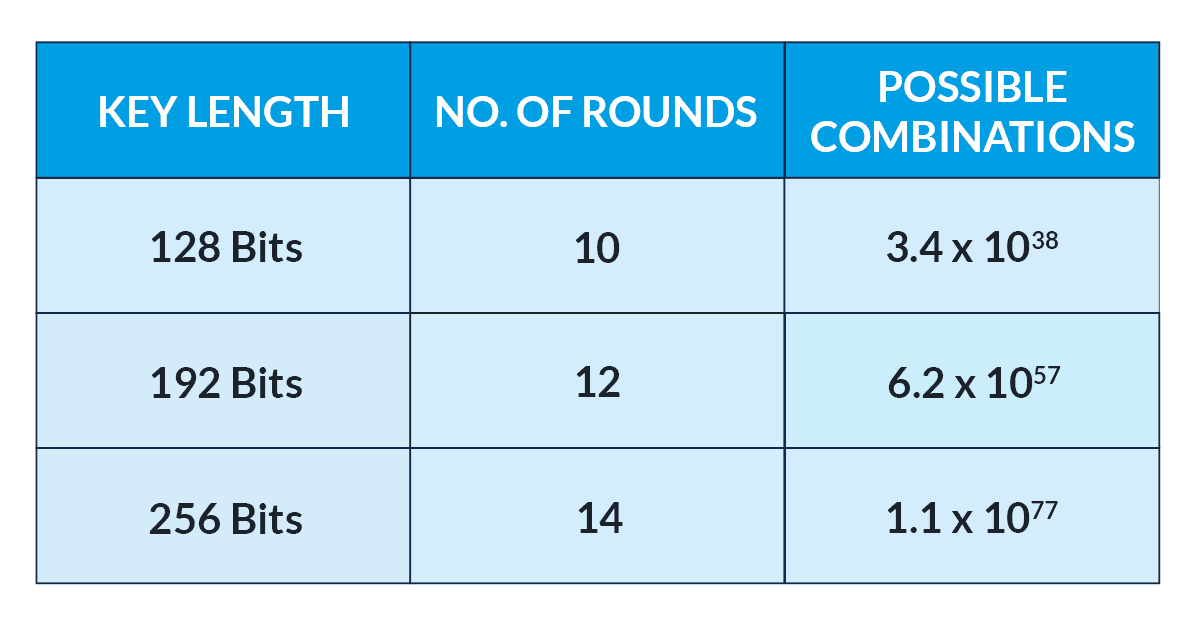
Most applications use a 128-bit key length, while governments or other entities dealing with highly sensitive or classified information use 192-bit encryption as well as the 256-bit key length, which is often referred to as 'military-grade' encryption.
Why not use the 256-bit key length for everything? Because 256-bit encryption requires more computing power, which can drain power sources faster and use up a lot of resources. Plus, 128-bit encryption is more than adequate protection for the majority of applications.
What Is AES Used For?
AES is integrated into many technologies we use for everyday functions, including:
- Wireless networks (Wi-Fi)
- Virtual Private Networks (VPNs)
- Password managers
- Programming language libraries
- File compression programs
- Mobile applications
- OS system components
- Hard drives
- Video games
This list gives you a good idea of how entrenched this encryption method is in our lives and our technology infrastructure.
What Are the Advantages of AES?
AES has become one of the most popular encryption tools around the world thanks to its combination of relative simplicity and strength. Its top features include:
1.) Easy Implementation - The encryption process is easy for IT experts and teams to understand, making AES extremely accessible.
2.) Ample Support - Developers and cyber security experts can call on a large support ecosystem, including frameworks, software libraries, manuals and other resources.
3.) Speed and Efficiency - Because it requires less memory than other methods, the algorithm quickly encrypts and decrypts data, making it suitable for use in fast-paced environments and meeting today’s expectations for speedy downloads.
4.) Versatility - The different key sizes offer flexibility in selecting the level of security for various applications. Plus, AES can be combined with other security protocols or types of encryption to provide an extra layer of security.
5.) Standardization - AES has been widely accepted and endorsed around the world, supporting greater compatibility across platforms and systems.
The Future of AES
While the security and strength of AES have been proven many times over, the advent of quantum computing technology presents new challenges. NIST has already announced several quantum-resistant algorithms for potential future use.
However, its experts are confident that AES will serve as a highly reliable encryption method for decades to come.
How We Use AES to Protect Your Backups
At Macrium, our products can offer two main lines of defence against malware, such as ransomware.
Users of Macrium Reflect and Site Manager and can opt to use AES encryption to protect their backup files.
In addition, Macrium Image Guardian (MIG) is a feature of Reflect, Site Manager and SiteDeploy. Granting write access only to Macrium tools, MIG blocks unauthorized modifications of your backup files.
Together with the option to use AES encryption, these features make it virtually impossible for malware, such as ransomware, to access your backups.
Try Macrium Reflect for Free
See MIG and our AES encryption options in action - download a free 30-day trial of Macrium Reflect for your business or for home use.

Previous Post
5 Ways You Can Protect Your Backups From Ransomware
Next Post
How Ransomware Works - A Guide for Small Businesses