Don’t Pay The Ransom! What the Experts Say About Responding to Extortion
In 2023, 66% of businesses worldwide were reported to have experienced a ransomware attack in the 12 months prior. In response, they ideally would have had an offline backup ready to go. They would then use this to perform a restore of their data and systems to get their operations back up and running as quickly as possible.
But as the news headlines continue to show, businesses of all sizes and sectors around the globe continue to be caught out by this particularly destructive type of malware.
Ransomware: To Pay or Not to Pay?
If your business finds itself in this situation, it may be tempting to consider paying the ransom. This is, of course, exactly what the cyber criminals who infected your systems want you to do.
However, experts, official bodies and law enforcement agencies almost unanimously agree that businesses should never, ever pay ransoms demanded of them by criminals and gangs. This is what they have to say and why.
National Cyber Security Centre (NCSC)
Remit: UK
Pay the Ransom? No
Advice: The NCSC repeatedly states that "law enforcement does not encourage, endorse nor condone the payment of ransom demands."
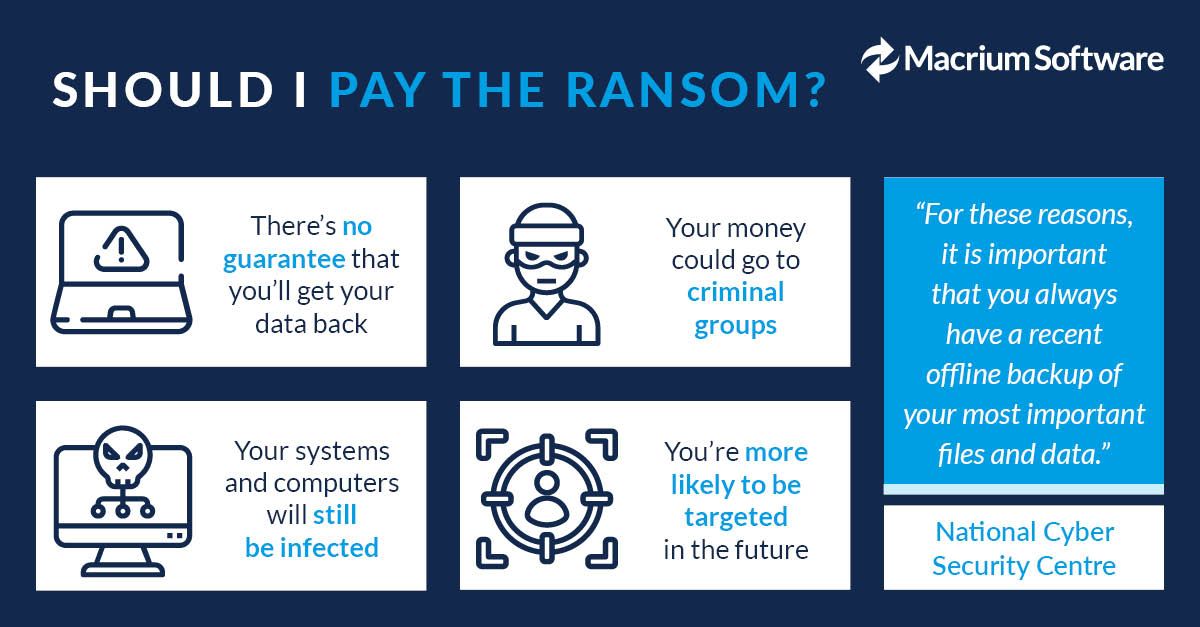
Why not Pay? The NCSC lists four good reasons for not paying:
- There's no guarantee that you'll regain access to your data
- Your endpoints will still be infected
- You'll be paying criminal groups
- You're more likely to be targeted in future
The Cybersecurity and Infrastructure Security Agency (CISA)
Location: USA
Pay the Ransom? No
Advice: Official advice is explicit, "CISA recommends that you do not pay the ransom." It goes on to state that "Paying ransoms doesn’t pay off."
Why not Pay? CISA lists several reasons for not paying ransoms. "Paying the ransom does not guarantee an organization will regain access to its data. In fact, some individuals or organizations [are] never provided with decryption keys after having paid a ransom."
The Federal Bureau of Investigation (FBI)
Location: USA
Pay the Ransom? No
Advice: The FBI's ransomware advice is clear - "The FBI does not support paying a ransom in response to a ransomware attack. Paying a ransom doesn’t guarantee you or your organization will get any data back. It also encourages perpetrators to target more victims and offers an incentive for others to get involved in this type of illegal activity."
Why Not Pay? The FBI cautions that paying the ransom doesn't guarantee you'll be given the decryption key. "Paying a ransom emboldens the adversary to target other organisations for profit and provides for a lucrative environment for other criminals to become involved."
The National Security Agency (NSA)
Location: USA
Pay the Ransom? No
Advice: Writing as part of the Joint Ransomware Task Force (JRTF), the NSA states that the "authoring organisations do not recommend paying ransom."
Why Not Pay? "Paying ransom will not ensure your data is decrypted, that your systems or data will no longer be compromised, or that your data will not be leaked." The NSA also warns that "paying ransoms may pose sanctions risks".
Australian Signals Directorate (ASD)
Location: Australia
Pay the Ransom? No
Advice: Perhaps the clearest guidance from any national body comes from the ASD - "Never pay a ransom".
Why Not Pay? The ASD states that "there is no guarantee you will regain access to your information, nor prevent it from being sold or leaked online. You may also be targeted by another attack."
Government of Canada
Location: Canada
Pay the Ransom? No
Advice: The Canadian Government's advice is slightly milder - "Paying the ransom is not usually advised."
Why Not Pay? The Canadian Government lists the following reasons not to pay a ransom:
- It will not guarantee you access to your files, as threat actors may demand more money, despite receiving the first ransom payment.
- It encourages threat actors to continue infecting your devices, or those of other organisations, with ransomware as they assume you will continue to pay with each attack.
- Threat actors can use wiper malware that masquerades as ransomware to alter or permanently delete your files once the ransom is paid, making them unrecoverable.
- Your data has likely been copied and the threat actor can leak it for profit or use it to continue to extort you.
- Your payment may be used to support other ransomware attacks or terrorist organisations.
What the Experts Say
Cyber security experts take a similar stance to the above bodies.
Bill Mew, Founder and CEO of Cyber SimulAItion and leading global campaigner for privacy and digital ethics, highlights the risk that ransom payments may eventually be seen as just another business expense.
"Such normalisation needs to be avoided at all costs," he explains. "Once these attacks are seen as just another business cost, people will start to take cyber security less seriously and it might become harder to justify spending money to protect against ransomware."
In her paper Cyber Security for Humans, Professor Victoria Baines, cyber security expert, former Europol Officer and Professor of IT at Gresham College, writes "Even if only a few of us pay the ransom, the criminal makes a profit."
She continues, "Law enforcement agencies naturally do not want criminal groups to make any more money and the US government has even suggested that victims who pay the ransom may be liable to prosecution. It’s my opinion that it’s part of our civic duty not to pay the ransom."
In his article 'Ransomware: 8 Things That You Must Know', cyber security leader, expert witness and author Joseph Steinberg points out that "Paying a demanded ransom may not get you your files back and may not prevent a leak of your information."
"Over the past half decade we have seen, repetitively, that, many crooks utilizing ransomware are not honest and that many parties who have paid ransoms have not regained access to their files."
Prevention Is Best When There Is No Cure
So, there it is - most official bodies and experts agree that businesses should firmly avoid paying cyber criminals. They also advise that the best way to avoid becoming a victim is to prepare your defences in advance.
Once ransomware has infected your systems and data, there's only one reliable way to recover them - restoring from a backup. Read our previous blog post for five ways you can protect your backups from ransomware.
Watch our Ransomware Webinar
Discover more about mitigating ransomware threats and gain advice on keeping your backups safe from ransomware. Watch our on-demand webinar for practical guidance and tips from us and cyber security expert James Bore of Bores Security.

9 Reasons Why You Should Never Pay Ransomware Attackers
What is Data Exfiltration and How Can it Harm Your Business?




